aleks.moleski@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
aleksander.malinowski@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
anatol.baranski@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
anton.plonski@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
ben.moore0622@outlook.com | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
edward.harley@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
iwan.banicki@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
johnwilson0825@outlook.com | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
kevin.brock@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
richard.francis10@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
robert.radwanski@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
roman.bobinski@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
roman.ulanski@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
stefan.moleski@mail.io | email | malware | N/A | N/A | Used for malware distribution on freelance developer platforms | Year in Review |
taraslysenko@mail.io | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
corresol28@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
corresol28@outlook.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
paniker1110@outlook.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
walterjgould77@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
supernftier@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
bohuslavskyir@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
artizjusz11@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
bartonfratz@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
cryptodev26@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
deinsulabasil@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
elsaadanifaiek@hotmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
felipe.debarros@hotmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
geordiecuppaidge684@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
greatbusinessman517@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
jhmnuykbvgftrss@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
kainmcguire@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
kimberlysunshine137@yahoo.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
konovalov1256@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
kvashinalexander@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
markstevemark85@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
oleksandrbokii963@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
paniker1110@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
rubenbolanos19733@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
simpsonkeith686@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
sonniehutley5@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
tagi238761@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
vlulepet9@gmail.com | email | malware | N/A | N/A | DPRK malware developer accounts | Year in Review |
cnova.business.en@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
danielmcevily.business918@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
jaimetru003@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
daysabethtederstz7533@hotmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
thiagocosta199295@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
cptrhzv09@hotmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
chainsaw1107@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
mutsabsaskajgig0f@outlook.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
snowl3784@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
dieterwang@proton.me | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
cesarpassos4808@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
lazar.master.0204@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
lujancamryn405@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
harryjason19880502@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
fraserhutchison1@hotmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
stovbanoleksandr14@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
ramirezhector9299@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
mimoriokamoto@gmail.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
wilson.wen2145@outlook.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
jasonfissionawgyi08293@outlook.com | email | malware | N/A | December 2025 | DPRK malware distributor GitLab.com account | Year in Review |
olelangaard9@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
mirandacunningham1993@outlook.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
jerryjames1997@outlook.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
caryphillips.business727@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
soft.business1103@outlook.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
soft.business1024@outlook.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
soft.business1020@outlook.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
soft.business0987@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
alphabrownsapon70555@hotmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
welbykchamu4i72@outlook.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
eron4236@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
reddixyxzh551438@hotmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
soft.business1112@outlook.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
richardcook.business93@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
jamesgolden198852@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
erik423131@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
alfredogomez1984126@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
jasonharris198852@gmail.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
xavieryetikqpir36636@outlook.com | email | malware | N/A | November 2025 | DPRK malware distributor GitLab.com account | Year in Review |
marcello.armand.tf7@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
gabriel.sanchez255@outlook.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
aronlin712@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
rickcarr1014@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
sallydunnet.business1016@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
dr.md.hubert.business916@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
tommyrole0301@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
jbutton717@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
lilian.rodrigues.re@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
andrewtilley.us@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
davidaheld.manager@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
lovelysong0209@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
moreandmore082@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
meirjacob727@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
harry.work206@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
abdelrahman5520032019@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
karenhooi.cpa.cga.business1016@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
craigsmith93.business@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
paulodiego0902@outlook.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
faelanholtmdjld41341@outlook.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
encar.geric727510@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
irynalavreniuk38@gmail.com | email | malware | N/A | October 2025 | DPRK malware distributor GitLab.com account | Year in Review |
melnikoleg995@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
opalinsigniagyprt29567@hotmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
thorneaustinngzsz52979@outlook.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
joshuataub3@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
itspeterszabo@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
xylosmontagueujsvt83787@hotmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
ivicastojadin488@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
seed1996017@outlook.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
bryandev0418@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
ruslanlarionov77@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
superdev@outlook.com.au | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
cristhianmartinezrom7@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
natasa.golubovic90@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
weili.walk@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
afaq91169@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
mahmodghnaj1@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
look.as.united@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
rochaevertondev@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
tabishhassan01998@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
temorexviashvili17@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
vovalishcn77@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
seed1996015@outlook.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
suryaedg88@hotmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
maurostaver9@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
pleasemeup214@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
vitalii214.ilnytskyi@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
reactangulardev@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
skyearth711@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
migueljose81234@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
seed1996010@outlook.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
blackwang104@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
kagan.hungri@gmail.com | email | malware | N/A | September 2025 | DPRK malware distributor GitLab.com account | Year in Review |
littebaby232355@gmail.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
kenycarl92@gmail.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
arnas.tf7@gmail.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
nandawsu58@hotmail.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
magalhaesbruno236@gmail.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
martytowne03@gmail.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
peter@trovastra.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
martinez@trovastra.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
peterforward@trovastra.com | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
rick.cto@dantelabs.us | email | malware | N/A | August 2025 | DPRK malware distributor GitLab.com account | Year in Review |
tomgleeson92@outlook.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
huqyyitizomu@hotmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
tracykevin5590@gmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
seniorsky92@gmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
meftaht531@gmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
tapiasamjann@gmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
johnwatson2327a@gmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
donald.edler0626@gmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
chrisritter5272@outlook.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
hs8179189@gmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
dredsoft@proton.me | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
bloxdev1999@outlook.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
star712418@gmail.com | email | malware | N/A | July 2025 | DPRK malware distributor GitLab.com account | Year in Review |
jackson.murray.tf7@gmail.com | email | malware | N/A | June 2025 | DPRK malware distributor GitLab.com account | Year in Review |
hudsonramsey107@outlook.com | email | malware | N/A | June 2025 | DPRK malware distributor GitLab.com account | Year in Review |
samjanntapia@gmail.com | email | malware | N/A | June 2025 | DPRK malware distributor GitLab.com account | Year in Review |
dyup58725@gmail.com | email | malware | N/A | June 2025 | DPRK malware distributor GitLab.com account | Year in Review |
davidfernandez420@outlook.com | email | malware | N/A | May 2025 | DPRK malware distributor GitLab.com account | Year in Review |
scottdavis8188@gmail.com | email | malware | N/A | May 2025 | DPRK malware distributor GitLab.com account | Year in Review |
samjannt1211@gmail.com | email | malware | N/A | April 2025 | DPRK malware distributor GitLab.com account | Year in Review |
ahmed03010229@gmail.com | email | malware | N/A | April 2025 | DPRK malware distributor GitLab.com account | Year in Review |
hidranomagica@outlook.com | email | malware | N/A | March 2025 | DPRK malware distributor GitLab.com account | Year in Review |
jackson.blau.eth@gmail.com | email | malware | N/A | February 2025 | DPRK malware distributor GitLab.com account | Year in Review |
agne09541@gmail.com | email | malware | N/A | February 2025 | DPRK malware distributor GitLab.com account | Year in Review |
antontarasiuk0512@gmail.com | email | malware | N/A | February 2025 | DPRK malware distributor GitLab.com account | Year in Review |
michael.dilks8500@gmail.com | email | malware | N/A | January 2025 | DPRK malware distributor GitLab.com account | Year in Review |
ignacioquesada127@gmail.com | email | malware | N/A | January 2025 | DPRK malware distributor GitLab.com account | Year in Review |
http://chainlink-api-v3.cloud/api/service/token/3ae1d04a7c1a35b9edf045a7d131c4a7 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
http://chainlink-api-v3.cloud/api/service/token/792a2e10b9eaf9f0a73a71916e4269bc | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
http://chainlink-api-v3.com/api/service/token/1a049de15ad9d038a35f0e8b162dff76 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
http://chainlink-api-v3.com/api/service/token/7d6c3b0f7d1f3ae96e1d116cbeff2875 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
http://chainlink-api-v3.com/api/service/token/b2040f01294c183945fdbe487022cf8e | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
http://openmodules.org/api/service/token/f90ec1a7066e8a5d0218c405ba68c58c | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
http://w3capi.marketing/api/v2/node/d6a8d0d14d3fbb3d5e66c8b007b7a2eb | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api-server-mocha.vercel.app/api/ipcheck-encrypted/106 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api-server-mocha.vercel.app/api/ipcheck-encrypted/212 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api-server-mocha.vercel.app/api/ipcheck-encrypted/81 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api-server-mocha.vercel.app/api/ipcheck-encrypted/823 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api-server-mocha.vercel.app/api/ipcheck-encrypted/99 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.mocki.io/v2/8sg8bhsv/tracks/errors/665232 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/159a15993f79c22e8ff6 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/62755a9b33836b5a6c28 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/b1f111907933b88418e4 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/b68a5c259541ec53bb5d | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/c82d987dd2a0fb62e87f | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/d1ef256fc2ad6213726e | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/d4dfbbac8d7c44470beb | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/e6a6bfb97a294115677d | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/f4be0f7713a6fcdaac8b | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://api.npoint.io/f96fb4e8596bf650539c | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://astraluck-vercel.vercel.app/api/data | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://bs-production.up.railway.app/on | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://getApilatency.onrender.com/checkStatus | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://getpngdata.vercel.app/api/data | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://googlezauthtoken.vercel.app/checkStatus?id=S,T | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://ip-api-test.vercel.app/api/ip-check-encrypted/3aeb34a38 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://ip-check-server.vercel.app/api/ip-check-encrypted/3aeb34a37 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/4NAKK | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/8RLOV | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/CNMYL | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/DMVPT | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/E4YPZ | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/E7GKK | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/FM8D6 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/GLGT4 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/L4T7Y | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/PCDZO | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/PQPTZ | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/WCXNT | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/XRGF3 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jsonkeeper.com/b/XV3WO | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://jwt-alpha-woad.vercel.app/api | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://metric-analytics.vercel.app/api/getMoralisData | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://pngconvert-p0kl4fodi-jhones-projects-f8ddbcbe.vercel.app/api | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/linux?flag=3 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/linux?flag=5 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/linux?flag=8 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/mac?flag=3 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/mac?flag=5 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/mac?flag=8 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/windows?flag=3 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/windows?flag=5 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/windows?flag=5 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-config-settings.vercel.app/settings/windows?flag=8 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load-config.vercel.app/settings/linux?flag=3 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load-config.vercel.app/settings/mac?flag=3 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load-config.vercel.app/settings/windows?flag=3 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/linux?flag=2 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/linux?flag=4 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/linux?flag=9 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/mac?flag=2 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/mac?flag=4 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/mac?flag=9 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/windows?flag=2 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/windows?flag=4 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://vscode-load.vercel.app/settings/windows?flag=9 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://web3-metric-analytics.vercel.app/api/getMoralisData | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
https://zone-api-navy.vercel.app/api/ip-check/99 | url | malware | N/A | N/A | JavaScript malware dropper URL | Year in Review |
passport-google-auth-token | npm package | malware | N/A | N/A | Malicious NPM dependency used to deliver malware | Year in Review |
dotenv-extend | npm package | malware | N/A | N/A | Malicious NPM dependency used to deliver malware | Year in Review |
tailwindcss-animation-advanced | npm package | malware | N/A | N/A | Malicious NPM dependency used to deliver malware | Year in Review |
seeds-random | npm package | malware | N/A | N/A | Malicious NPM dependency used to deliver malware | Year in Review |
chai-jsons | npm package | malware | N/A | N/A | Malicious NPM dependency used to deliver malware | Year in Review |
dotenv-intend | npm package | malware | N/A | N/A | Malicious NPM dependency used to deliver malware | Year in Review |
preset-log | npm package | malware | N/A | N/A | Malicious NPM dependency used to deliver malware | Year in Review |
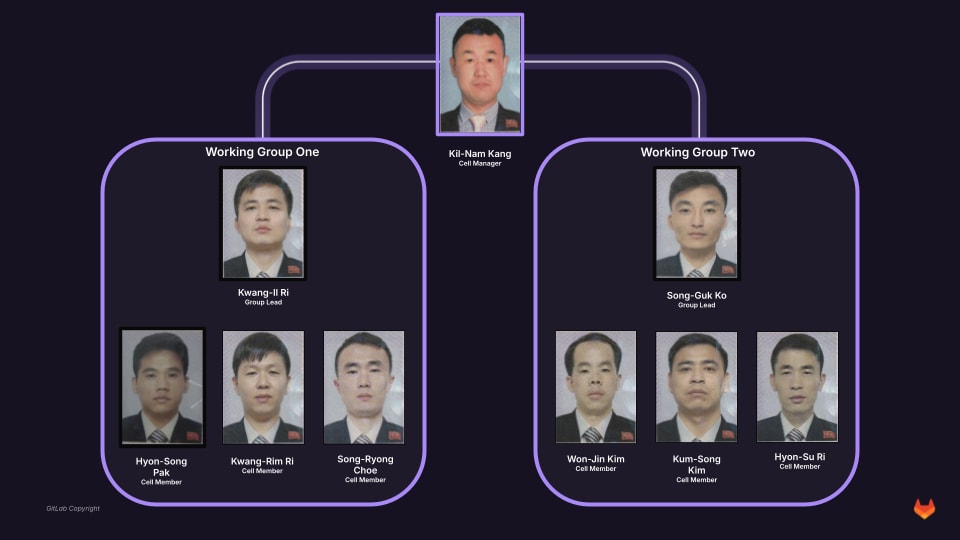
111.197.183.74 | ipv4 | insider | October 2025 | October 2025 | Originating IP address of Kil-Nam Kang | 1 |
alancdouglas@googlemail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
alphatech1010@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
amitnyc007@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
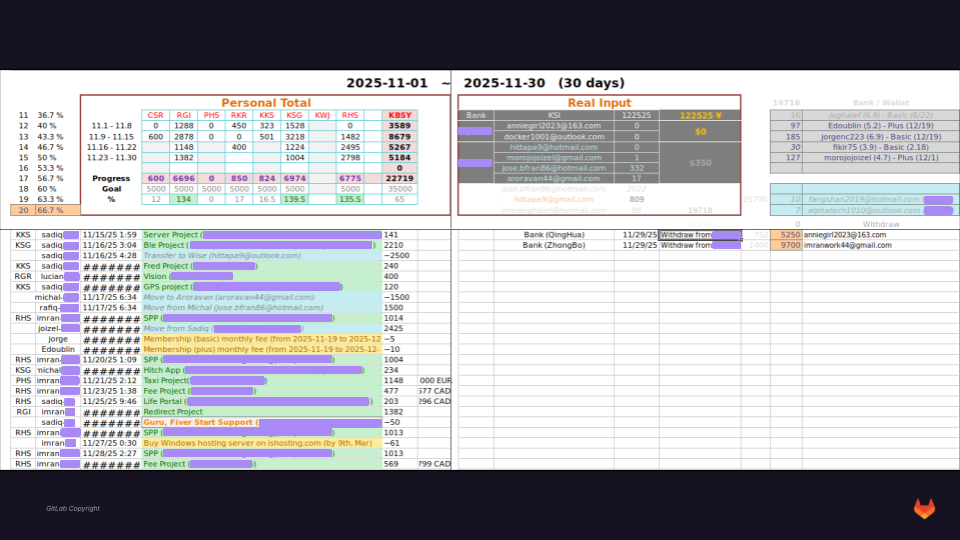
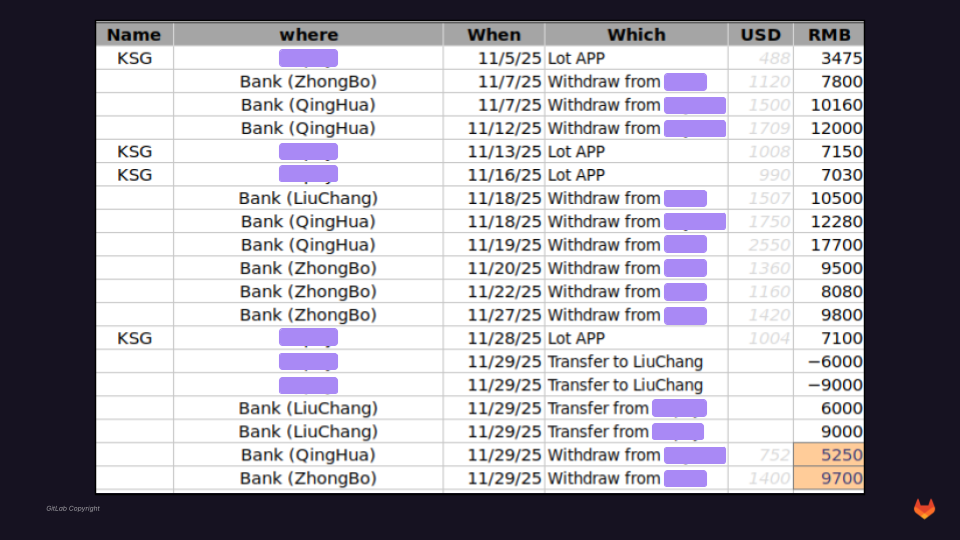
anniegirl2023@163.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
appyleonardo77@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
awmango123@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
bowavelink@163.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
cpduran0622@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
docker1001@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
elvialc620@163.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
emilyvanessaaa@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
enrique122528@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
erasmusmadridtrops@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
ericdoublin1111@yahoo.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
eruqulpuaro@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
eruqulpuaro@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
eruqulpuaro1@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
eruqulpuaro1@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
fangshan2019@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
goldstar0906@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
gtracks.onelink@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
happycoder1111@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
happyleonardo77@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
hittapa9@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
housinginmadrid@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
imadjeghalef@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
imranwork44@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
indulgenight@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
janeisman@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
janeisman21@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
jingya0131@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
jinkonachi@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
joizelmorojo@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
jorgencnc0608@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
jorgencnc0608@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
jorgencnc960608@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
jose.bfran86@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
jose.bfran86@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
k_star_0131@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
kbsy2019@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
khatijha555@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
kk14s@ya.ru | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
knightrogue414@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
konachi0531@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
kosong0926@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
kosong0926@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
lava_0208@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
leonardo_perez@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
li.guangri.2020@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
lovinmadrid@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
marza0219@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
mazheng225@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
michael-mardjuki@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
michael.getz28@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
onepushsing@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
owaisugh75@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
paku_2018@yahoo.co.jp | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
pohs0131@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
r_gi_19950603@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
r_gi19950603@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
raphael.privat@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
rhs0219@hotmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
rksonava1@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
rodev097@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
silverbead0815@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
silverbead0815@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
su0220@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
superth55@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
truelife3188@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
vickydev1018@outlook.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
victm1121@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
wangsmithsilverstar@gmail.com | email | insider | N/A | N/A | Threat actor-controlled email | 1 |
8613341122552 | phone number | insider | N/A | N/A | Mobile number of China-based cell member | 1 |
8618811177571 | phone number | insider | N/A | N/A | Mobile number of China-based cell member | 1 |
8617701222967 | phone number | insider | N/A | N/A | Mobile number of China-based cell member | 1 |
8618911321235 | phone number | insider | N/A | N/A | Mobile number of China-based cell member | 1 |
8619910229812 | phone number | insider | N/A | N/A | Mobile number of China-based cell member | 1 |
8613381035676 | phone number | insider | N/A | N/A | Mobile number of China-based cell member | 1 |
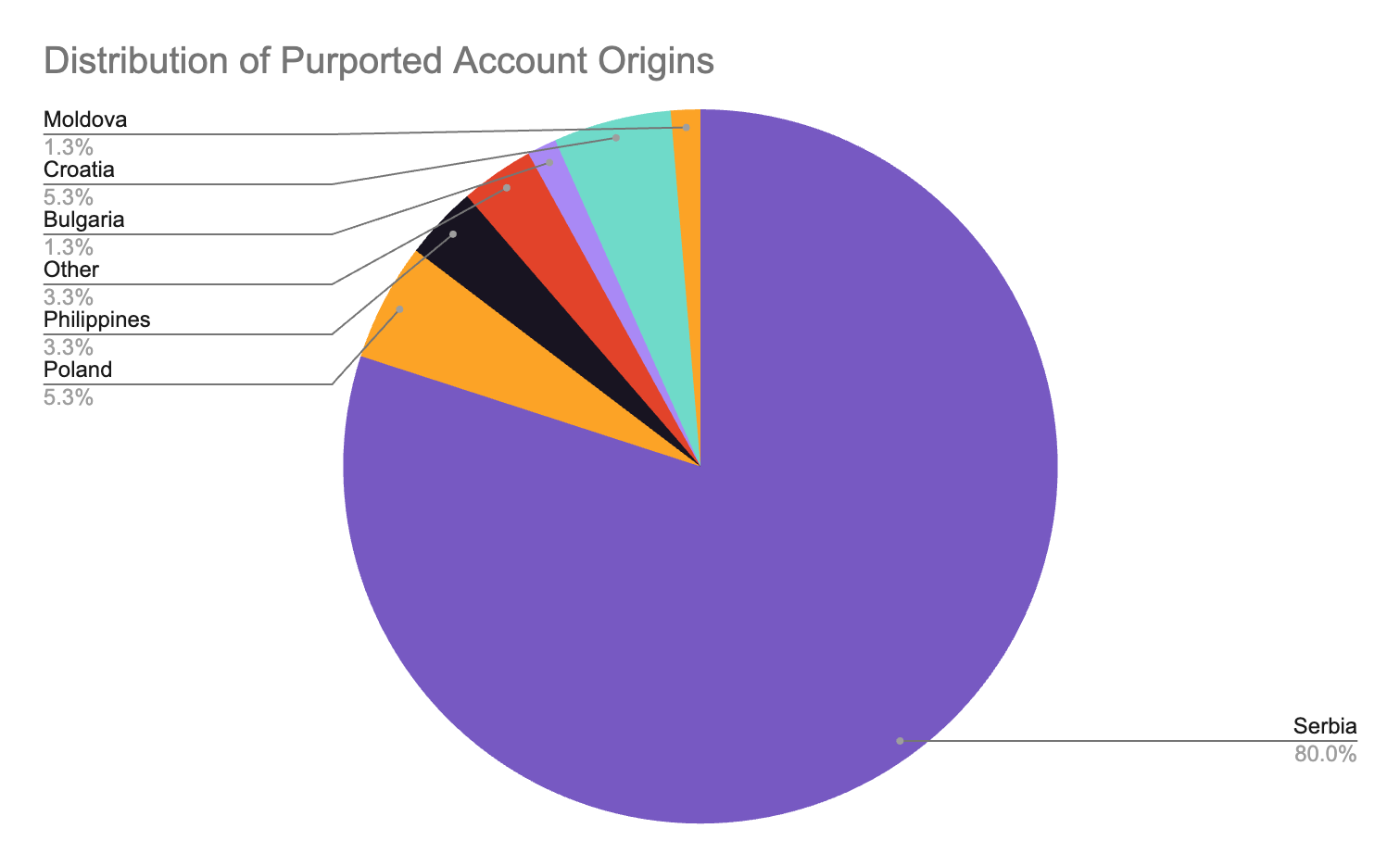
tinsimonov@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
bogomildaskalov001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
blazhejovanovska@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
sarloevtim39@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
antonisharalampopoulos@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
aleksandarradakovic122@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
krstoilovski@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
filipbackus@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
belarosviska@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
ladislav.kvarda525@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
novskapetar@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
peceyurukov@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
nikolamilev166@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
emil.rysinov@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
vinkolukac.dev@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
valentincinika@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
bosevskibale6@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
vlanosdimitri001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
PeterVargova@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
vlastimirdeskov001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
aidaszvikas@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
trendafilmakedonija001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
dmitrycebotari@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
chrisgergo00@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
briangaida12@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
wiktor.rogal@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
michalcopik1@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
albertdymek@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
dobromirkovachev@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
toma.andric@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
danielmonilis@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
vladimirvoski001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
kolyotroske001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
borissudar.cro@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
bodorbenci@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
ivoloucky@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
yorgosdulev@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
balazspapp@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
juliankopala.pol@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
nanusevskitodor@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
ediurmankovic.cc@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
vuksanbojanic@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
barry__johnson@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
gary__leduc@hotmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
adamikjelen@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
ionguzlok@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
antonijakub11@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
leonidasnefeli@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
alexandrurusu2@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
adrianceban1@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
florinbarbu1@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
danielsala2@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
ivanhorvat2@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
nikolastojanovski2@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
gabrieltamas1@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
victorajdini@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
gavrilvasilevski001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
stojannastevski001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
emirapolloni@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
gorantomik1@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
jonasvarga1@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
dzholedinkov001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
LaszloEniko@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
lazarbulatovic56@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
emilkokolnska@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
iacovlevguzun@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
dovydasmatis@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
tomaskovacova@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
antoninowak12@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
erikslamka1@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
kostasmichalakakou@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
jokubasbieliauskas1@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
stoilesideropoulos001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
damjandobrudzhanski@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
kutayijaz@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
simeondimitris001@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
bobituntev001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
velyokazepov@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
nestorovskiemilija100@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
ankaankahristov@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
randoviska@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
borislavbabic431@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
benicdominik81@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
teoantunovic6@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
popovicjelena727@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
vaskovdime@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
jozefmtech@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
archelaosasani@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
janlindberg80@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
nevenborisov@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
toni.komadina@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
damianwalczak.work@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
denis.dobrovodsky@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
filip.lovren@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
tomislavjurak@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
emilijan.hristov@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
zoran.parlov@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
ivanmatic.fs@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
marcelpaw.lowski@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
tomislavbozic.work@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
dominik.wojk@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
piotrglowacki.pol@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
leonzielinski.pol@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
stanislav.timko@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
oleg.kaplanski@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
rafael.ratkovic@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
mateusz.moczar@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
nadoyankovic@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
dionizy.kohutek@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
emilsvalina@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
kostic.gordan@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
josipbraut@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
mirantrkulja@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
pavlehristov.work@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
vedranpodrug@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
zvonkobogdan.cr@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
filipdamevski001@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
albertoszlar52@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
benjaminellertsson@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
fedorkadoic@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
izakholmberg12@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
markusvillig20@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
reigojakobson45@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
masudtarik69@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
vaikokangur45@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
osogovskiplanini001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
aleksonikov001@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
angelovaandreev@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
ivanopavic13@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
davorsabolic2@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
juricleon407@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
kondradgodzki@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
velizarborisov.fs@outlook.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
trivuniliikc519@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
alexandermori1218@gmail.com | email | insider | N/A | N/A | Synthetic persona email | 2 |
smupyknight@outlook.com | email | insider | N/A | N/A | DPRK developer email | 2 |
btrs.corp@gmail.com | email | insider | N/A | N/A | DPRK developer email | 2 |
byolate@gmail.com | email | insider | N/A | N/A | DPRK developer email | 2 |
starneit105@gmail.com | email | insider | N/A | N/A | DPRK developer email | 2 |
chrissamuel729@gmail.com | email | insider | N/A | N/A | DPRK developer email | 2 |
lozanvranic@gmail.com | email | insider | N/A | N/A | DPRK developer email | 2 |
qoneits@outlook.com | email | insider | N/A | N/A | DPRK developer email | 2 |
kitdb@outlook.com | email | insider | N/A | N/A | DPRK developer email | 2 |
d.musatovdv@gmail.com | email | insider | N/A | N/A | DPRK developer email | 2 |
nikola.radomic322@gmail.com | email | insider | N/A | N/A | DPRK developer email | 2 |
duykhanh.prodev@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
chebiinixon91@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
jeffukus@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
mohamed_dhifli@hotmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
saputranady@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
ryannguyen0303@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
fahrultect@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
patrickjuniorukutegbe@rocketmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
fahrultech@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
mirzayevorzu127@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
tsunaminori@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
yhwucss@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
btrs.corp@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
ledanglong@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
cwertlinks@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
bukoyesamuel9@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
gwanchi@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
efezinoukpowe@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
thnam0107@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
vijanakaush@gmail.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
luis.miguel208@outlook.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
smupyknight@outlook.com | email | insider | N/A | N/A | Git mirror developer identity | 2 |
brankojovovic99@gmail.com | email | insider | N/A | N/A | Administrative/testing accounts on abused services | 2 |
manuetuazon.work@gmail.com | email | insider | N/A | N/A | Administrative/testing accounts on abused services | 2 |
upwork.management.whm@outlook.com | email | insider | N/A | N/A | Administrative/testing accounts on abused services | 2 |
1.20.169.90 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
103.106.112.166 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
103.152.100.221 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
103.155.199.28 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
103.174.81.10 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
103.190.171.37 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
103.39.70.248 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
107.178.11.226 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
107.189.8.240 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
113.160.133.32 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
115.72.1.61 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
117.1.101.198 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
121.132.60.117 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
125.26.238.166 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
139.178.67.134 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
14.225.215.117 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
143.110.226.180 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
144.217.207.22 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
146.190.114.113 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
147.28.155.20 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
148.72.168.81 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.229.34 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.229.42 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.229.46 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.229.47 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.229.83 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.229.86 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.229.93 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.231.42 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.231.83 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.231.86 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.231.93 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
152.26.231.94 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
153.92.214.226 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
157.245.59.236 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
171.228.181.120 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
171.99.253.154 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
172.105.247.219 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
173.255.223.18 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
178.63.180.104 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
179.1.195.163 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
184.168.124.233 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
193.227.129.196 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
193.38.244.17 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
194.104.136.243 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
194.164.206.37 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
195.159.124.57 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
195.85.250.12 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
2.59.181.125 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
200.24.159.153 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
200.60.20.11 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
203.150.128.86 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
204.12.227.114 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
222.252.194.204 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
222.252.194.29 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
23.237.145.36 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
31.41.216.122 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
34.122.58.60 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
37.210.118.247 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
37.46.135.225 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
38.158.202.121 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
38.183.146.125 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
4.7.147.233 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
45.119.114.203 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
45.144.166.24 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
45.189.252.218 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
45.81.115.86 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
47.220.151.116 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
50.6.193.80 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
51.159.75.249 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
54.37.207.54 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
57.128.201.50 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
61.198.87.1 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
64.92.82.58 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
64.92.82.59 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
67.43.227.226 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
67.43.227.227 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
67.43.228.253 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
67.43.236.19 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
67.43.236.20 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
72.10.160.171 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
72.10.160.92 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
72.10.164.178 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
74.255.219.229 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
82.180.146.116 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
94.23.153.15 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
95.182.97.53 | ipv4 | insider | August 2024 | November 2024 | Threat actor proxy address (may be shared origin) | 2 |
ryan.service.1001@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 3 |
dmbdev800@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 3 |
kari.dev1217@gmail | email | insider | N/A | N/A | Threat actor persona email | 3 |
iamjanus66@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 3 |
4696382784 | phone number | insider | N/A | N/A | Threat actor persona phone number | 3 |
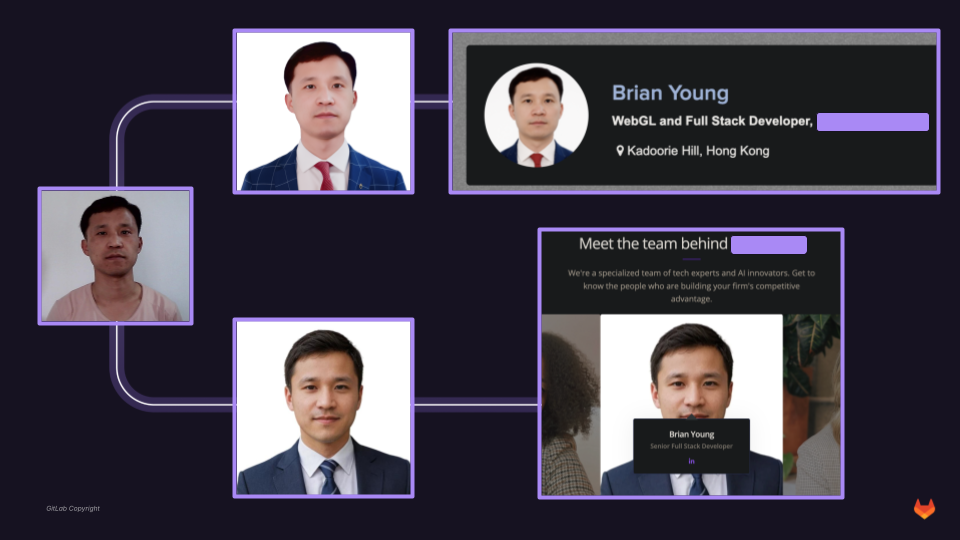
brianyoung.luck@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
brianyoung0203@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
codingwork.dev@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
jinwangdev531@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
gdavisiv.dev@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
nicolas.edgardo1028@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
alexeilucky23@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
aleksey0753@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
develop498@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
4899432@qq.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
karsonova1703@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
maximmironenkoreact@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
vitalyandronuke@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
alexeysamsonofff@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
realnitii1@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
devnitin18@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
alexiyevaj@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
initinbhardwaj@yahoo.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
anna.putinarus@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
rajukumar127.dev@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
kekisevu@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
anastasiaanufriyenko@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
naterongi@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
andriimalyshenko@yahoo.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
gabrygreg1@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
luckydev2289@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
forfuture21@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
darbylee923@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
alexei.lee0203@outlook.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
yuriassasin0603@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
luis.lee.tech@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
bryanjsmiranda@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
luislee.software@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
panda95718@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
givometeq@mentonit.net | email | insider | N/A | N/A | Threat actor persona email | 4 |
maradanod.favomubo@vintomaper.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
humblechoice.dev@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
jairoalberto2208@hotmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
quxiujun520520@163.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
igorslobodyan508@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
brianyoung.lucky@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
valerykrapiv@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
dveretenov@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
blbnlambert34@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
tezauidev@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
nicewitali0311@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
shopstar0907@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
rl6700907@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
naterongi1@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
alexeu005@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
versatile.skydev@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
kevinhelan2@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
cglobalpower923002@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
albertchess990919@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
lorenzo.vidal@mail.ru | email | insider | N/A | N/A | Threat actor persona email | 4 |
stolic5star@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
nkvasic5star@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
freelancer.honest.developer@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
viana.mabel3058@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
jairo.business392@yahoo.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
jairoacosta00123@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
ferwerwe6@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
maskymlap@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
alexsam.dev@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
kostiaberez369@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
darkrut22@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
jennalolly93@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
vikram.imenso@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
greg.work.pro@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
denish.faldu226@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
janeica.dev@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
mdmahdiuli@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
aronnokunjo@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
hadiulislam391@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
mahdi39980@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
mahdiupwork2002@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
mdmahdiul@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
wildbotgamer@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
tramendo.L@outlook.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
dyadkovdevelop@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
tramendo.M@outlook.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
Gulfdom0209@outlook.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
Wei861420@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
brianyoung0203@outlook.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
david@heyadev.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
mykytadanylchenko@outlook.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
ronaldofanclub112@gmail.com | email | insider | N/A | N/A | Threat actor persona email | 4 |
olegevgen@inbox.lt | email | insider | N/A | N/A | Threat actor persona email | 4 |
15414257086 | phone number | insider | N/A | N/A | Threat actor persona phone number | 4 |
89883507137 | phone number | insider | N/A | N/A | Threat actor persona phone number | 4 |
14358179097 | phone number | insider | N/A | N/A | Threat actor persona phone number | 4 |
3508704464 | phone number | insider | N/A | N/A | Threat actor persona phone number | 4 |
4796004206 | phone number | insider | N/A | N/A | Threat actor persona phone number | 4 |
5596103595 | phone number | insider | N/A | N/A | Threat actor persona phone number | 4 |